Starting with Linux can be daunting for longtime Windows or Mac OS X users, and just about everyone who has tried out Linux has had to adjust to the fact that you’re not meant to manage software like you’re used to. This often winds up frustrating users who try to reuse their tried-and-true methods in Linux which often leads to a poor user experience. However, if a new user is willing to learn the basics of how package management works in Linux, they’ll discover the greatest immediate usability improvement that Linux-based operating systems offer compared to their counterparts.
Keep reading for a detailed look at how software management differs on Linux and what users can expect in practical use.
Breaking Expectations
Managing Software on Windows
Windows users are accustomed to downloading a .exe or .msi file from the internet or a CD and running a setup wizard. This results in a new shortcut icon on the desktop and in the start menu, and uninstalling is usually performed either through the control panel or by a start menu entry. As of Windows 8 it seems that the future is moving toward an app store paradigm for managing software, but Windows is likely to retain the current methods for decades to come.
For upgrades, Windows users either rely on the application to automatically check for upgrades or they’ll have to manually check online for upgrades and reinstall that way. System upgrades are done through the Windows Update tool and notoriously frequently require a system restart. The hassle this process poses tends to leave Windows users with a large amount of out-of-date software which may have known security holes.
Managing Software on Mac OS X
Mac OS X users typically either install software from the Mac Store which shows up in the Applications menu or download a .dmg file which typically asks the user to drag and drop a shortcut to the Applications folder. Uninstalling applications is accomplished by dragging the application icon to Trash.
The upgrade situation for Mac OS X users is similar to Windows except that applications installed through the App Store are more readily upgraded automatically. Software installed manually through a .dmg file still needs to either check for updates by itself or be manually checked by the user just like Windows software installed by a .exe or .msi file. System upgrades are, like Windows with Microsoft, issued at the discretion of Apple and are issued separately from other software.
Linux: Enter Package Management
With very little exception, none of these paradigms describe managing software in Linux. Linux employs package managers do manage all software including system software (the Linux kernel, the bootloader, etc), software libraries (required for other software to function), and user applications (such as the VLC media player or the Firefox web browser). These packages are stored in repositories (repos) which are shipped with the distribution you install and can be changed. Package management is often touted by Linux users as one of the best reasons for using the platform if it otherwise suits one’s needs; what we’ll discover is a system that offers the following:
- All software installed with a package manager can be simultaneously upgraded with a single command or button click
- As long as you can trust the distribution’s repositories, all software you install is trustworthy (you can also choose to download the source code with package manager if that’s of interest)
- Installing, upgrading, and uninstalling is all handled through the same interface
- Particularly when using the command-line interfaces, installing software is predictable and can be automated; this makes setting up a fresh Linux install doable with a single script
- The only software upgrades that require a reboot to take advantage of are Linux kernel updates, and if one is using a long term support stable type of distribution these are probably infrequent
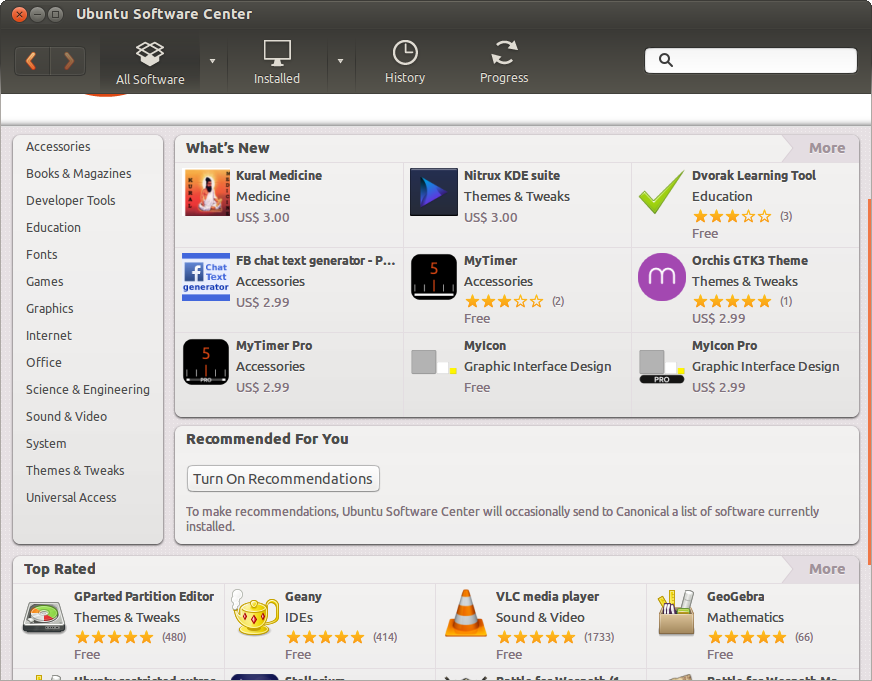
At their core, the package managers come in the form of command-line applications accessed from the terminal, and experienced Linux users often gravitate toward accessing them in this manner, but there are also numerous graphical interfaces for these package managers that are more accessible to the average user. For example, Ubuntu features the Ubuntu Software Center (pictured below) which uses the app store paradigm but is really just an interface for accessing packages in Ubuntu’s repositories using the apt package manager. There are lower-level graphical frontends like Synaptic that offer a lot of useful features but are slightly less user friendly than say the Ubuntu Software Center. As is generally the case, Linux never fails to offer vast freedom of choice.
Using Package Managers
I’ll focus on Ubuntu for the following examples due to the distribution’s market share and popularity among new users; the command-line instructions are common to Debian-based (and Ubuntu-based) distributions, and other package managers like yum and pacman function similarly on the command line. Also I’ll generally be foregoing exhaustive details; other easily Googleable guides do a great job of this for covering advanced functionality.
Graphical Package Managers
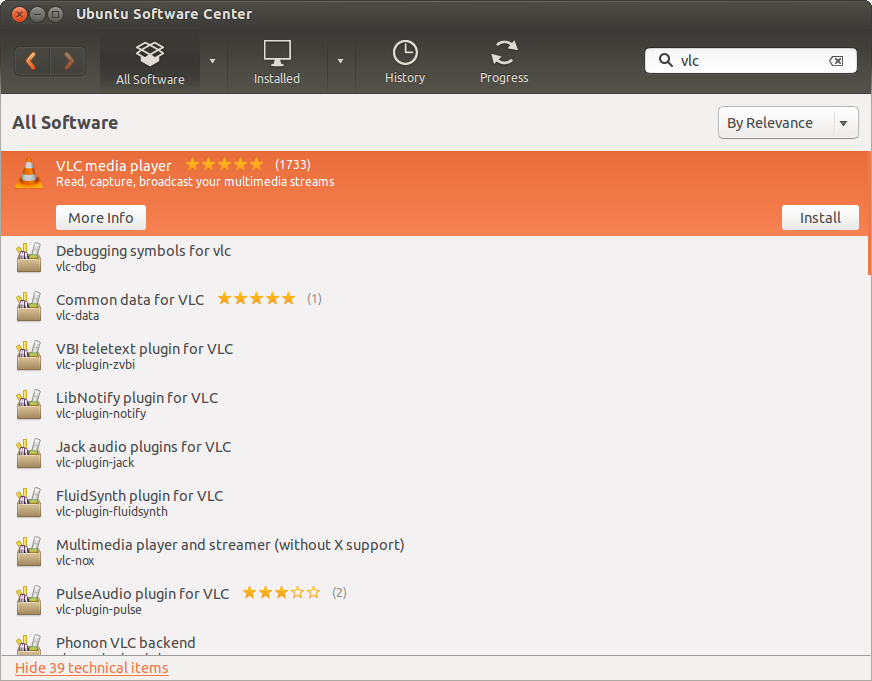
As noted above, graphical package managers on Linux such as the Ubuntu Software Center are trending toward the app store paradigm. You open up the interface, you are presented with a category list and/or a featured app list, and you may either browse the categories or search for software. For instance, the following Ubuntu Software Center screenshot shows sample search results for “vlc” which is a popular cross-platform video and audio player. This allows for a more familiar and user-friendly experience.
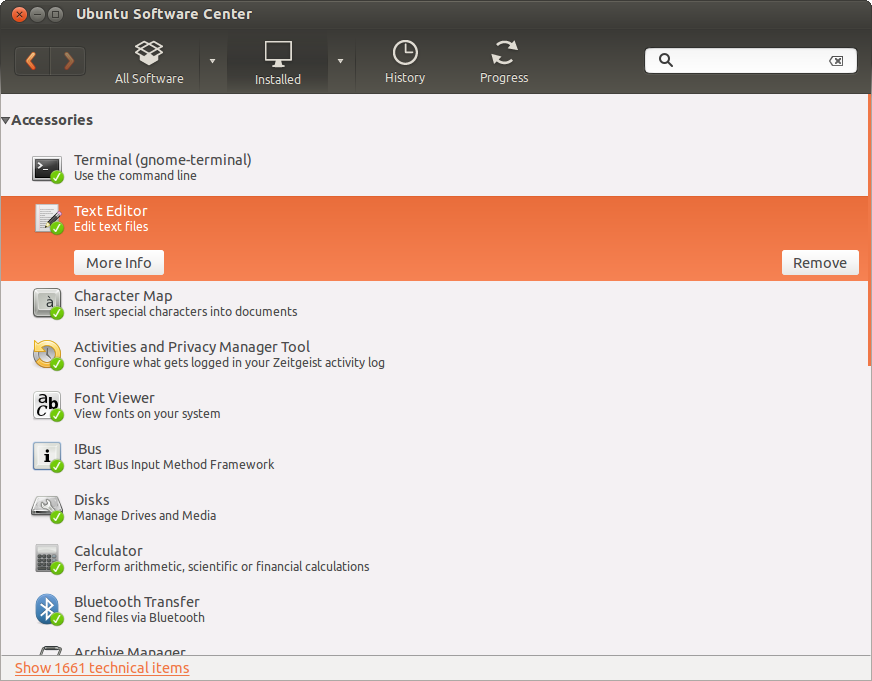
The Ubuntu Software Center, like most of its alternatives, allows the user to browse installed packages and remove items:
Searching is equivalent to searching through the repositories your package manager is configured to use; Ubuntu Software Center for example will use the apt package manager which, as with most things Linux, is also accessible via the command line. If a user chooses to add another repository, software found in this repository will become searchable in the graphical package manager.
The primary difference between using a Linux graphical package manager and, say, the Mac OS X App Store is that because of the all-reaching nature of Linux package managers and repositories, literally all system software is centralized in this graphical interface. That is, not only are user applications available but also core system software and libraries are available: the Linux kernel itself, bootloaders, and software libraries are all available to browse and install in addition to user applications like the VLC media player or the GIMP image editor. Again: in Linux all software is centralized rather than having a gap between system and user software.
Terminal Interface Package Managers
As is often the case with Linux, everything you can do in a graphical interface can be accomplished using command-line tools in the terminal; many experienced users find a high level of comfort and enhanced efficiency when working in the terminal. I’ll try and help illustrate how this can be the case by showing the basic functionality of the apt package manager.
First, one typically updates their package list by syncing with the repositories (other package managers bake this functionality in with other commands):
sudo apt-get update
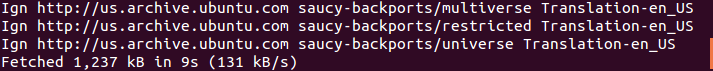
Notice that a lot of package management actions require root privileges which is why sudo was used here. In the sample output above the lines like saucy-backports/multiverse is an example of an Ubuntu repository. Now let’s look at probably the four most common apt functions:
Upgrade all installed packages
sudo apt-get upgrade
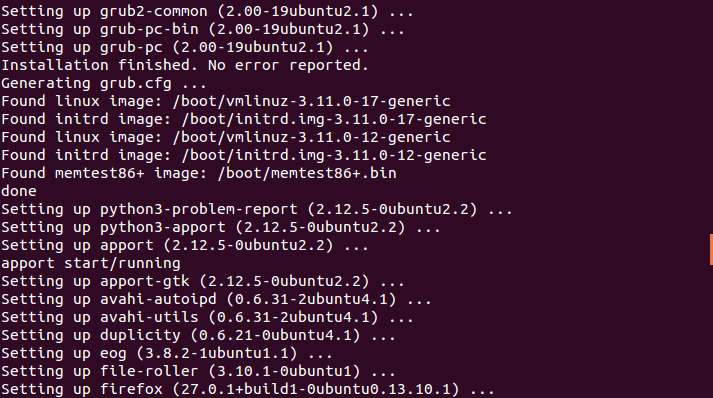
Notice how both firefox (a web browser, a user application) and grub2 (a bootloader, a core system application) are both handled by the same utility.
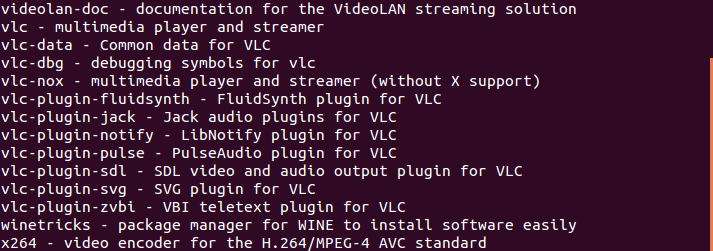
Search for a package (for example, VLC)
apt-cache search vlc
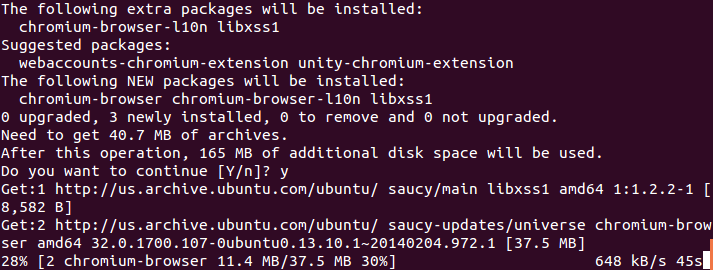
Install a package (for example, the Chromium web browser)
sudo apt-get install chromium-browser
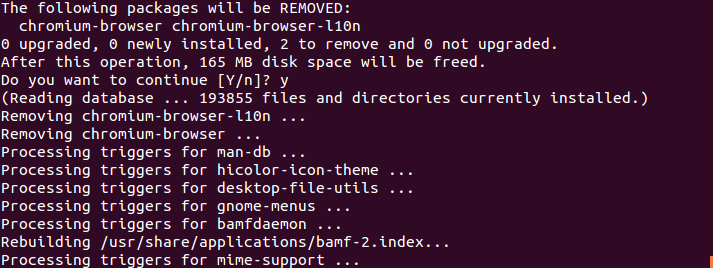
Uninstall a package (for example, the Chromium web browser)
sudo apt-get remove chromium-browser
Note here that one can install (or uninstall) many packages at once:
sudo apt-get install libreoffice-writer libreoffice-calc vlc chromium-browser
and so on. Immediately one powerful use is clear: one can write a script to run when they do a fresh install of their OS that installs… everything. It might look like:
1 2 3 4 5 6 7 8 9 10 | |
and here the \ was used to split a single command into multiple lines.
The Rare Case: Not Using Package Managers
While it’s uncommon for typical users, there is some software generally not found in a distribution’s repositories due to licensing or other legal issues, the distribution’s principles, or other reasons. On occasion software will be available on the web for download as a .deb file (or for RPM-based distributions a .rpm file) – this is a Debian package just like one would install using the apt package manager. The difference is software installed this way generally won’t be automatically upgraded with the rest of the system’s packages so this is more similar to installing a .exe or .dmg file in Windows or Mac OS X.
Installing software this way is pretty simple: download the .deb file and double click it in the file manager. Ubuntu will install this using the Ubuntu Software Center, and other distributions may come with other graphical alternatives like gdebi. Alternatively, one can use the command line:
sudo dpkg -i /path/to/package.deb
Again, software that is only available this way is rare. The most common case that I can think of is the proprietary Google Chrome browser (note that the open-source Chromium browser is essentially Chrome without certain proprietary Google built-ins, and this is typically found through the package managers of all major distributions). The interesting thing about this case is that when you install Google Chrome’s .deb package it also adds a repository so that upgrading through your package manager also upgrades Chrome, so in this case the only hassle is fetching the .deb package online. Other software may not do that and will need to be handled manually.
Closing Thoughts: A Case Example
As I started on my own Linux journey I quickly found myself frequently switching distributions (or distro-hopping), and early on this was mainly constrained to different Ubuntu flavors (Ubuntu, Xubuntu, Kubuntu, etc) every time a new release occurred on those exciting April and October days. It wasn’t too long until I discovered how easy it was to automate setting everything up cleanly again after another fresh install by writing a single shell script. A snippet of one of the scripts I used for setting up Ubuntu a while ago follows:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 | |
You can see how this script combines modifying certain system configurations, updating software repositories (through what is called a ppa in this case), and removing, upgrading, and installing packages all in the confines of one script. There are plenty of other more user-specific things one can include to set everything back up with a script like this, but the point here is how efficiently we can set up a system exactly how we want it thanks to Linux paradigms like package management and command-line utilities. I would encourage everyone to keep an open mind in this regard and see where their own explorations lead them.
]]>